Did you know crime will be responsible for 6 trillion dollars damage by 2021?
It’s critical to protect app data with Firebase Encryption, but first, we need to know what exactly is encryption.
Quick Jumps
What is Encryption?
Encryption is a way of protecting your data from malicious hackers, spy, and online criminals.
Thereby encryption is a mathematical algorithm that scrambles information into the complex ciphertext that can only be decoded by its recipient.
Related: Read All About Firebase Authentication
Still didn’t get it?
Encryption converts your understandable plain text to random text that a person can’t understand, even computers too—exception exists.
But What is Firebase Encryption?
Firebase Encryption is a way of protecting your app data with the help of Firebase, a product owned by Google, from hackers.
Simple, you can encrypt your user data inside the Firebase database.
Have you heard that HTTPS is a solution to every hacking attempt?
Nope, you’re wrong.
Here is what Aman Sood says about HTTPS:
The same is the case with your app, even if all the requests are processed with HTTPS, your app needs additional security and encryption.
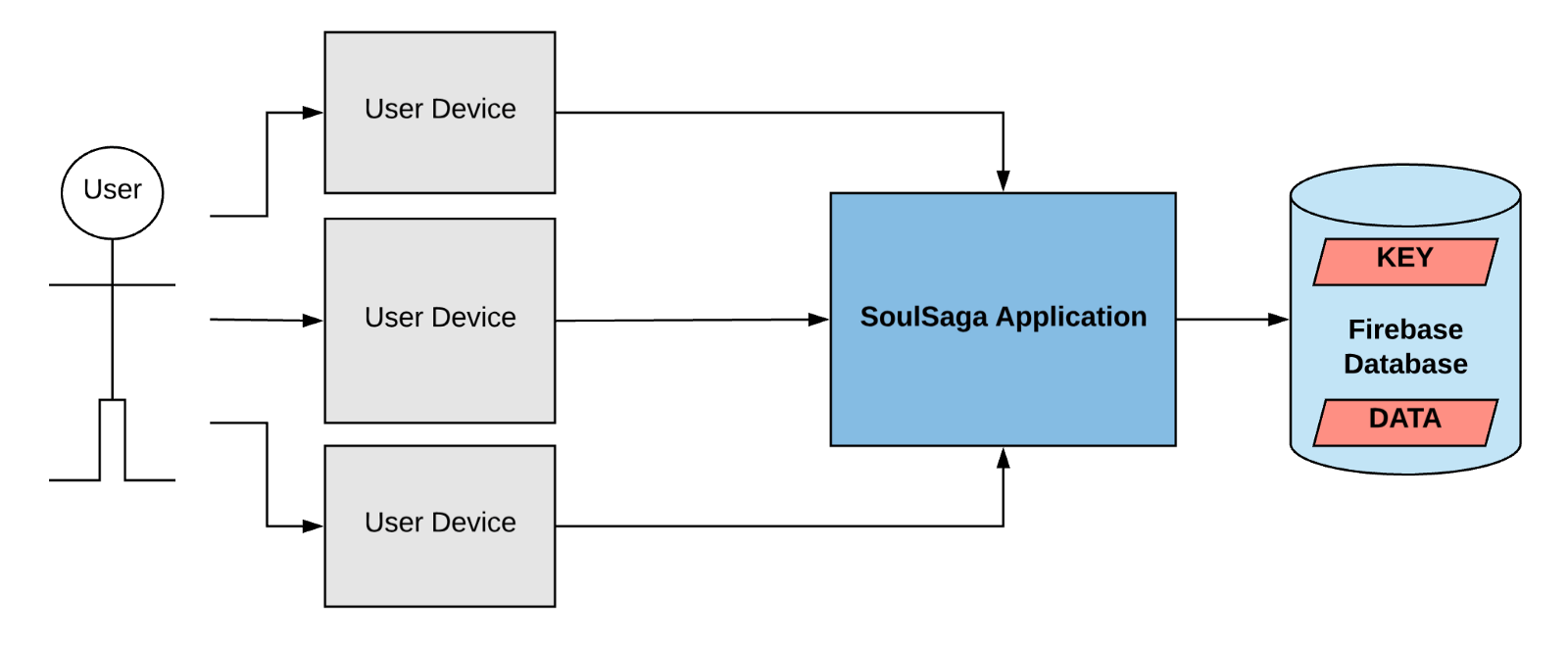
Moreover, Firebase Rest server routes your data to the backend database which also has all control over the data.
Even when the data is written in the disk, this is in the encrypted format and the encryption key is also available to Google. Further, the administrator of the app can see the content.
The worst problem?
As you know that Firebase is good at security, but you can say that it’s not great. You have seen news even the best apps get hacked and companies need to pay millions to hide.
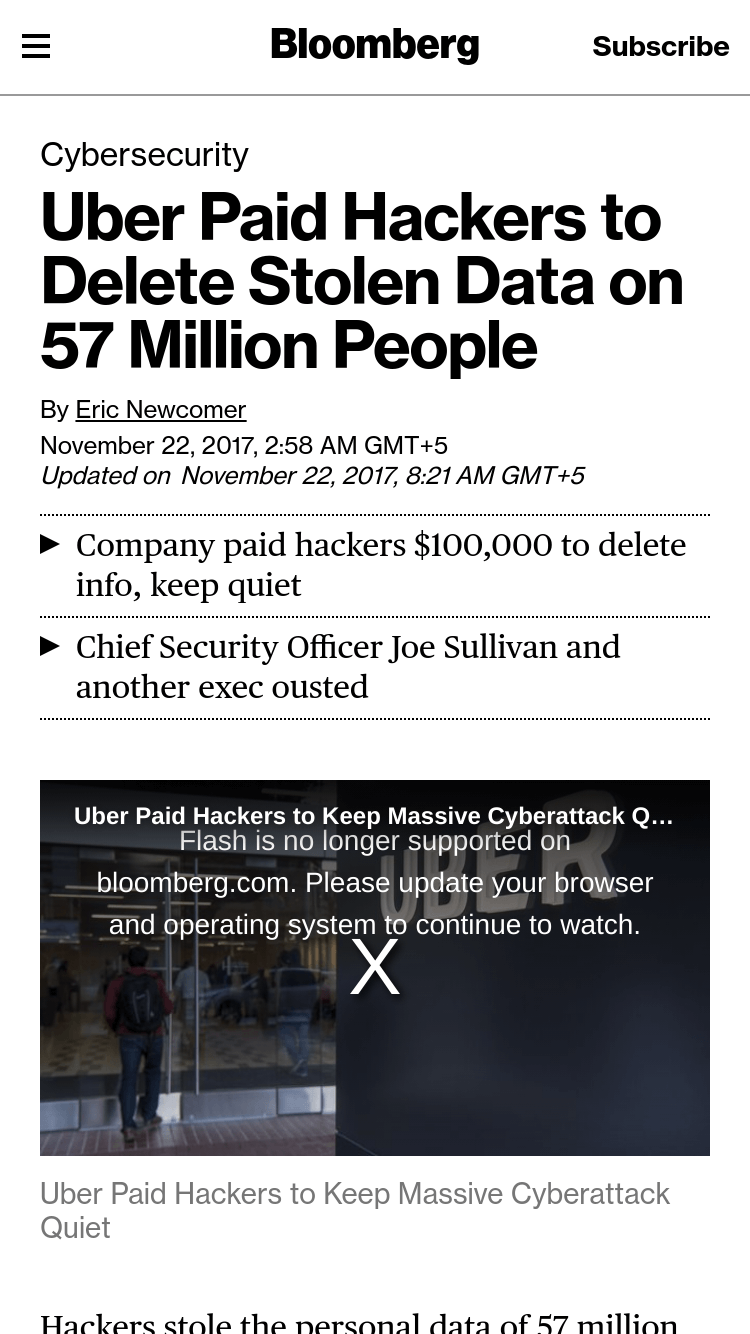
In addition, user trust compromises and needs full protection which Firebase can’t provide.
As you already know that WhatsApp provides end-to-end encryption which means ISP, third parties, even app owners aren’t able to see the data. isn’t it interesting?
In this article, I am discussing some of the scenarios where you can encrypt client-side encryption.
You can consider the final one for my best opinion
With the help of symmetric keys (with this key you can encrypt or decrypt both sides of data) like AES encryption and description is easy with some other existing libraries.
But the main issue is we have to find a reliable place where we can put these keys.
5 Ways to Protect Your Data with Firebase Encryption:
We’ve figured out the 5 ways to protect your data for the app you design with Firebase.
1. Store Key in Your Own Server:
If you’re going to save keys in your own server, you can use the keys to decrypt the data.
But the major problem is that it provides no security.
Hackers can hack your server and can also decrypt your data that’s why it is highly not recommended.
It’s recommended to get the server that is not easily hackable.
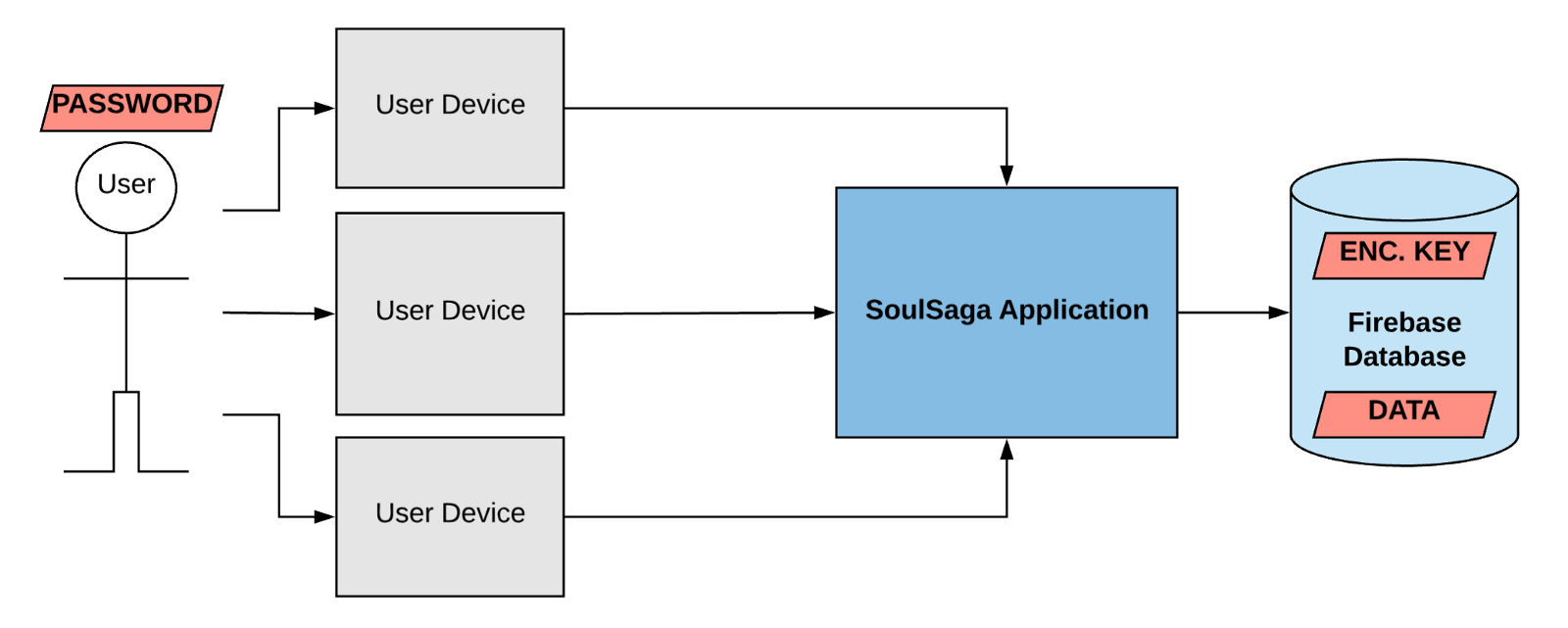
2. Encryption Key on Password:
You can either store keys on the server and ask the user to keep a good strong password in order to encrypt the keys.
But that scenario is not ideal because it requires work on sser’s end and if the user forgets it password then it’s impossible to recover.
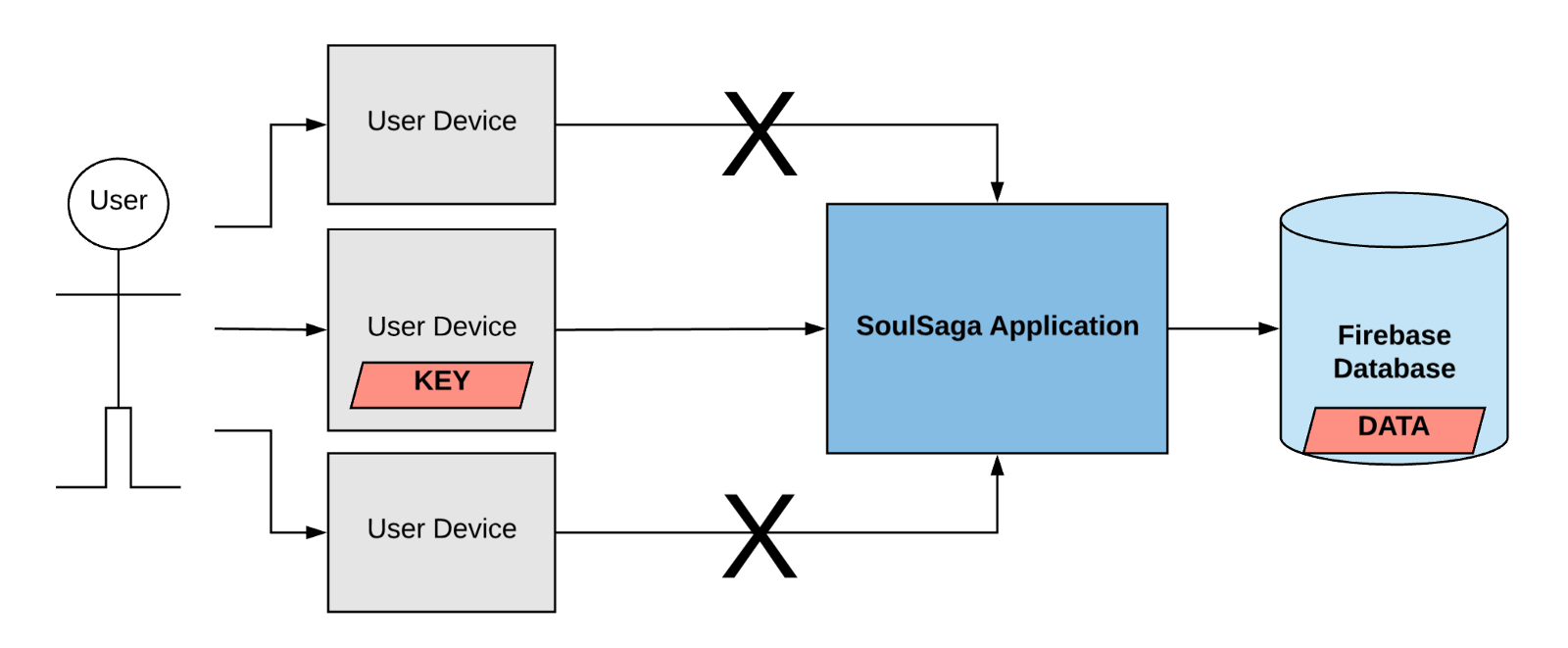
3. Store Key on User Own Devices:
This approach is exceptionally similar to end-to-end encryption, in this scenario, you can store the key on the user’s devices and the key is not available in the app servers.
The drawback of this scenario is that you can’t access the key and the data is not available on other devices.
This is not a bad approach depending on the circumstances, but it’s not what I am looking for.
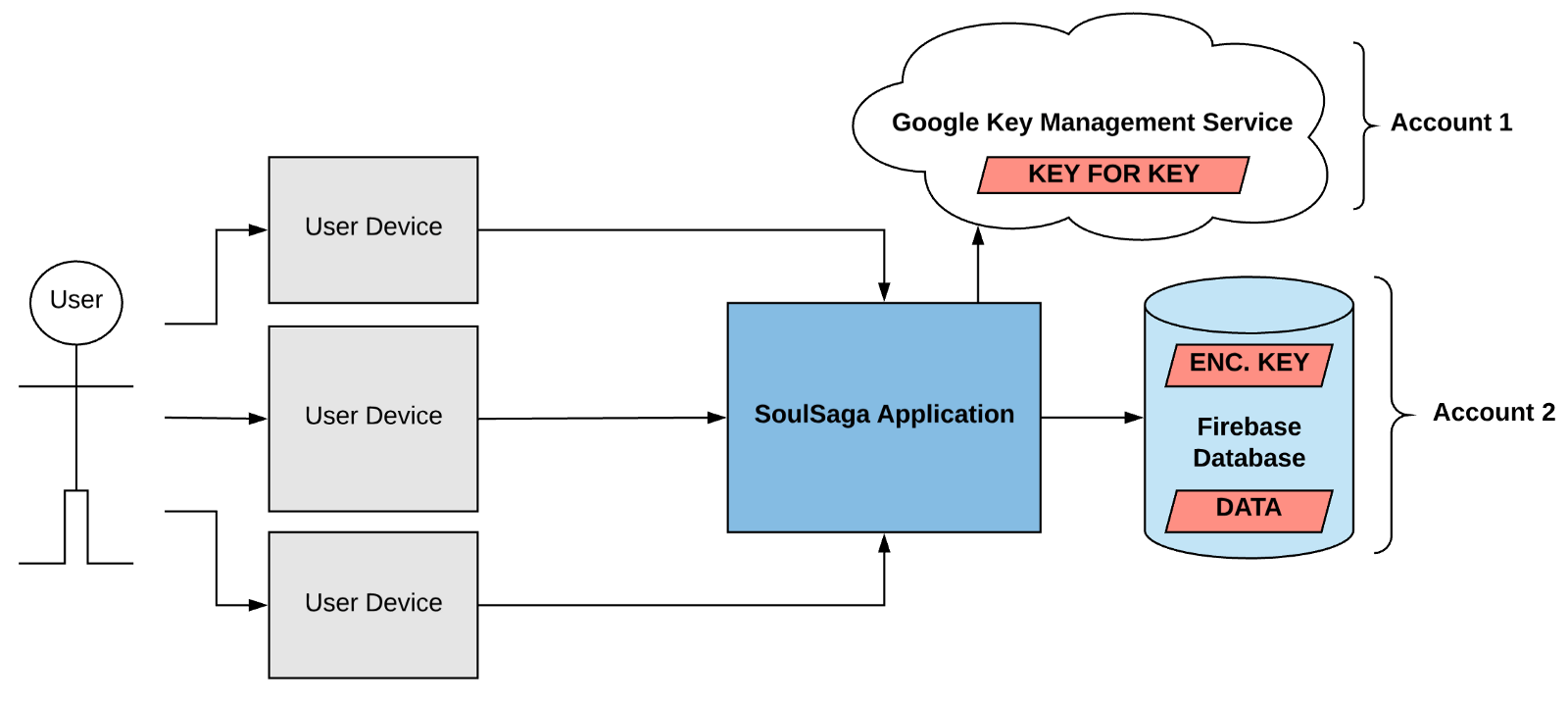
4. Use Google KMS for Key Encryption:
Google KMS is a cloud-hosted key management service that lets you manage cryptographic keys for your cloud services the same way you do on-premises.
It’s a popular solution presented by Andy Gears available on the market.
In this case, the key is encrypted with other data that is stored in Google KMS (Key Management Service).
The user’s key encrypts the user’s data and afterward, the key is being encrypted by Google KMS Key which is stored in the database.
I really want to design a system in the future.
NOTE: KMS key associates to a separate Google account to the Firebase database so that no user has the authority to read data & decrypt it.
Suppose if a hacker wants to access the data it should have to compromise both accounts
5. Hide Key in the User’s Google Account! (With User Acceptance):
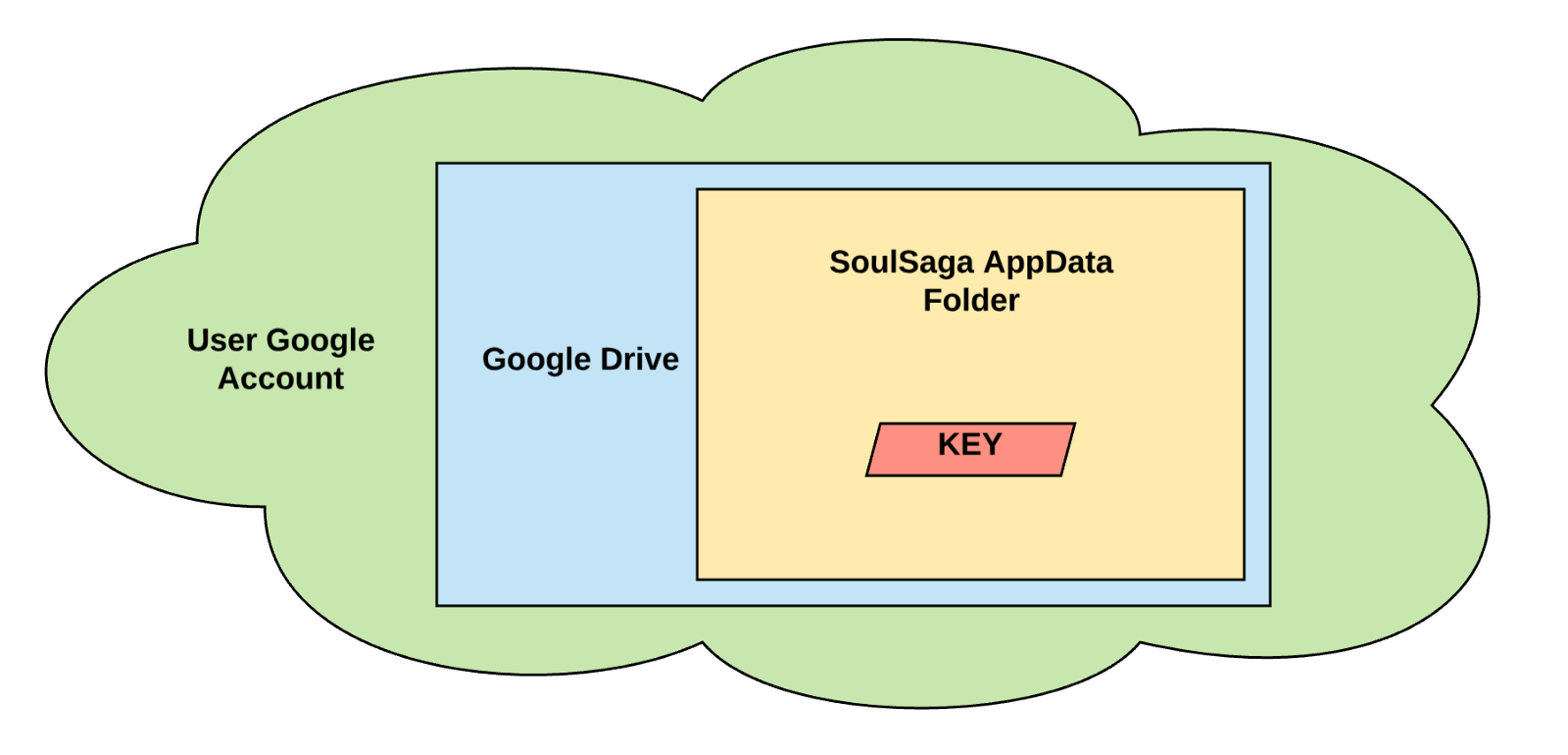
When a user logs in, then we get the OAuth (open authorization is the open-source auth framework for token authentication) credentials to request the user’s own encryption key.
Or you can create one if you can’t find one of the user’s Google accounts.
This way, the key is forever available in the user’s ownership, but they never deal with it directly.
If a hacker wants to get the key, then he should hack the user’s Google account then the hacker can read the data in the application.

Basically Google drive provides us an API just for producing a specific application data folder (here user permission is required) and the content of this folder is invisible to the users and it can only be accessed through the app’s credentials.